Electronics | Free Full-Text | Business Email Compromise Phishing Detection Based on Machine Learning: A Systematic Literature Review
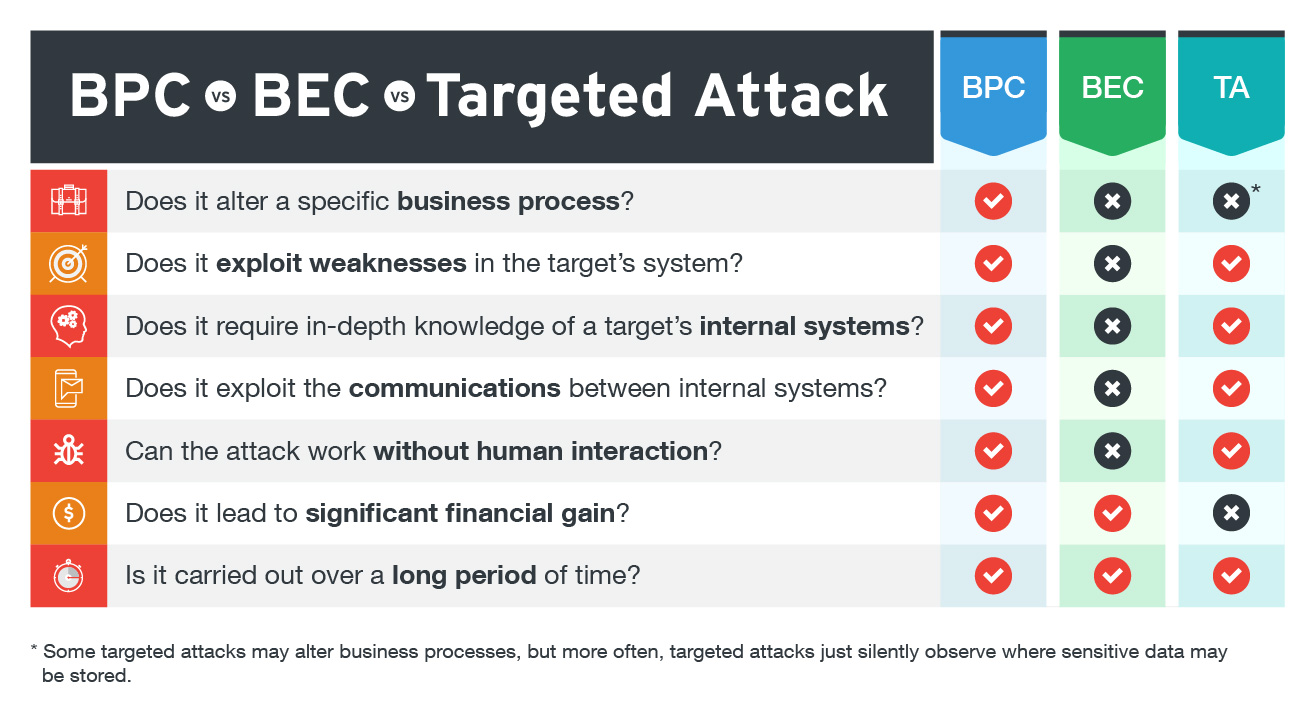
Business Process Compromise, Business Email Compromise, and Targeted Attacks: What's the Difference? - Security News

JCP | Free Full-Text | Business Email Compromise (BEC) Attacks: Threats, Vulnerabilities and Countermeasures—A Perspective on the Greek Landscape

How to Spot & Protect Against Business Email Compromise (BEC) Attacks - Hashed Out by The SSL Store™

Armorblox Email Security Threat Report Reveals 72% Rise in Business Email Compromise Attacks in 2022 | Business Wire

Business Email Compromise: Unmasking the Tactics Behind CEO Fraud and Prevention Strategies - Security Investigation




.png)